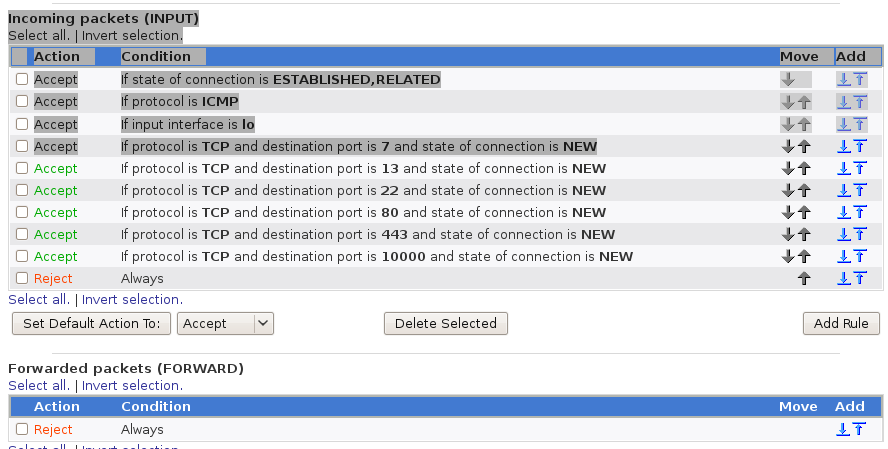
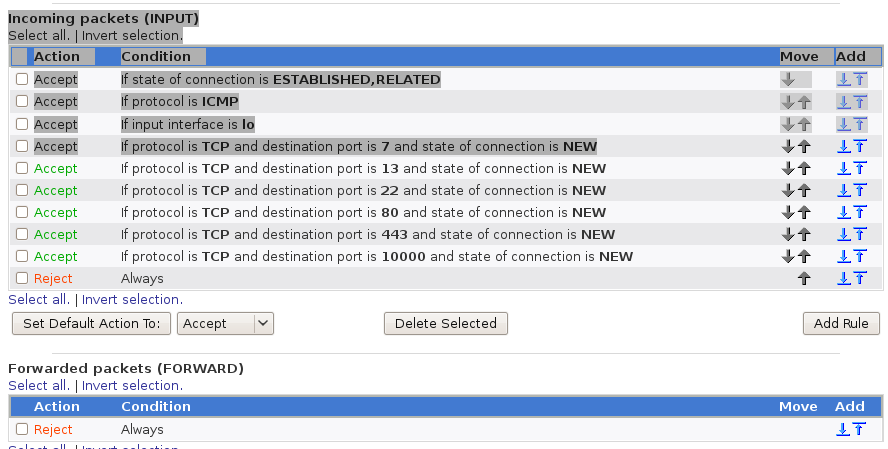
Webmin view of iptables
Organisations need security policies detailing roles, identities, authentication and authorisation
For example, there may be policies such as "No access will be permitted to the network from external sources and only Web access is allowed from internal to external sites and must pass through an institution Web proxy"
At the network boundaries, access policies are implemented by firewalls, which allow or disallow IP traffic based on ports, source and destination addresses and origin of TCP sessions
e.g. "the firewall will allow packets to pass in either direction belonging to TCP sessions originating internally on port 8080; all other TCP packets are blocked; all packets belonging to other protocols are blocked"
iptables allow you to set up a firewall on a Linux box
It allows you to accept or deny connections using any
protocol such as TCP, UDP, ICMP, SCTP, ...
(protocols are listed in /etc/protocols)
iptables passes packets through
A packet from outside destined for this machine passes through the INPUT chain
A packet from inside from this machine passes through the OUTPUT chain
A packet from outside forwarded from this machine to another interface passes through the FORWARD chain
You can see the state of your iptables configuration by
iptables -L
Each chain applies a table of actions
For packets from external to internal, you can perform
raw prerouting
mangle prerouting
mangle input
filtering
For packets from internal to external, you can perform
mangle output
NAT output
filter output
mangle postrouting
nat post-routing
For packets crossing from one interface to another you can perform
raw pre-routing
mangle pre-routing
nat pre-routing
mangle forward
filter forward
mangle post-routing
nat post-routing
A rule can specify a protocol, a port, interface, new or existing connection, direction, ...
A typical rule might be "new TCP connection inbound on interface eth0 on port 80"
An action is Accept or Reject
Rules are applied from top to bottom in each table
The last rule is usually "all reject", to block any packets not accepted by earlier rules
The chains apply to filter, mangle, nat, etc
Each component of a chain is organised into a table
The tables are filter, nat, mangle, etc
So e.g. the part of the INPUT chain dealing with filtering is put in the filter table as the INPUT entries
If iptables is not running, iptables -L will show
that everything is allowed through:
Chain INPUT (policy ACCEPT)
target prot opt source destination
Chain FORWARD (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination
If iptables is running and configured to only allow incoming
ssh connections, then
iptables -L will show
Chain INPUT (policy ACCEPT)
target prot opt source destination
ACCEPT all -- anywhere anywhere state RELATED,ESTABLISHED
ACCEPT icmp -- anywhere anywhere
ACCEPT all -- anywhere anywhere
ACCEPT tcp -- anywhere anywhere state NEW tcp dpt:ssh
REJECT all -- anywhere anywhere reject-with icmp-host-prohibited
Chain FORWARD (policy ACCEPT)
target prot opt source destination
REJECT all -- anywhere anywhere reject-with icmp-host-prohibited
Chain OUTPUT (policy ACCEPT)
target prot opt source destination
In FC11 the configuration is /etc/sysconfig/iptables
# Firewall configuration written by system-config-firewall
# Manual customization of this file is not recommended.
*filter
:INPUT ACCEPT [0:0]
:FORWARD ACCEPT [0:0]
:OUTPUT ACCEPT [0:0]
-A INPUT -m state --state ESTABLISHED,RELATED -j ACCEPT
-A INPUT -p icmp -j ACCEPT
-A INPUT -i lo -j ACCEPT
-A INPUT -m state --state NEW -m tcp -p tcp --dport 22 -j ACCEPT
-A INPUT -j REJECT --reject-with icmp-host-prohibited
-A FORWARD -j REJECT --reject-with icmp-host-prohibited
COMMIT
# Generated by webmin
*mangle
:FORWARD ACCEPT [0:0]
:INPUT ACCEPT [0:0]
:OUTPUT ACCEPT [0:0]
:PREROUTING ACCEPT [0:0]
:POSTROUTING ACCEPT [0:0]
COMMIT
# Completed
# Generated by webmin
*nat
:OUTPUT ACCEPT [0:0]
:PREROUTING ACCEPT [0:0]
:POSTROUTING ACCEPT [0:0]
COMMIT
# Completed
Rewrites IP addresses from a local network to the WAN
Commonly used in private networks - protects untrusted Windows machines from some external attacks by wrecking the end-to-end internet model :-)
NAT is handled by IP tables at the pre- or post-routing stage
Create an IP table called "nat" and add these lines:
nat -A POSTROUTING -o eth0 -j MASQUERADE
-A FORWARD -i eth1 -o eth0 -j ACCEPT